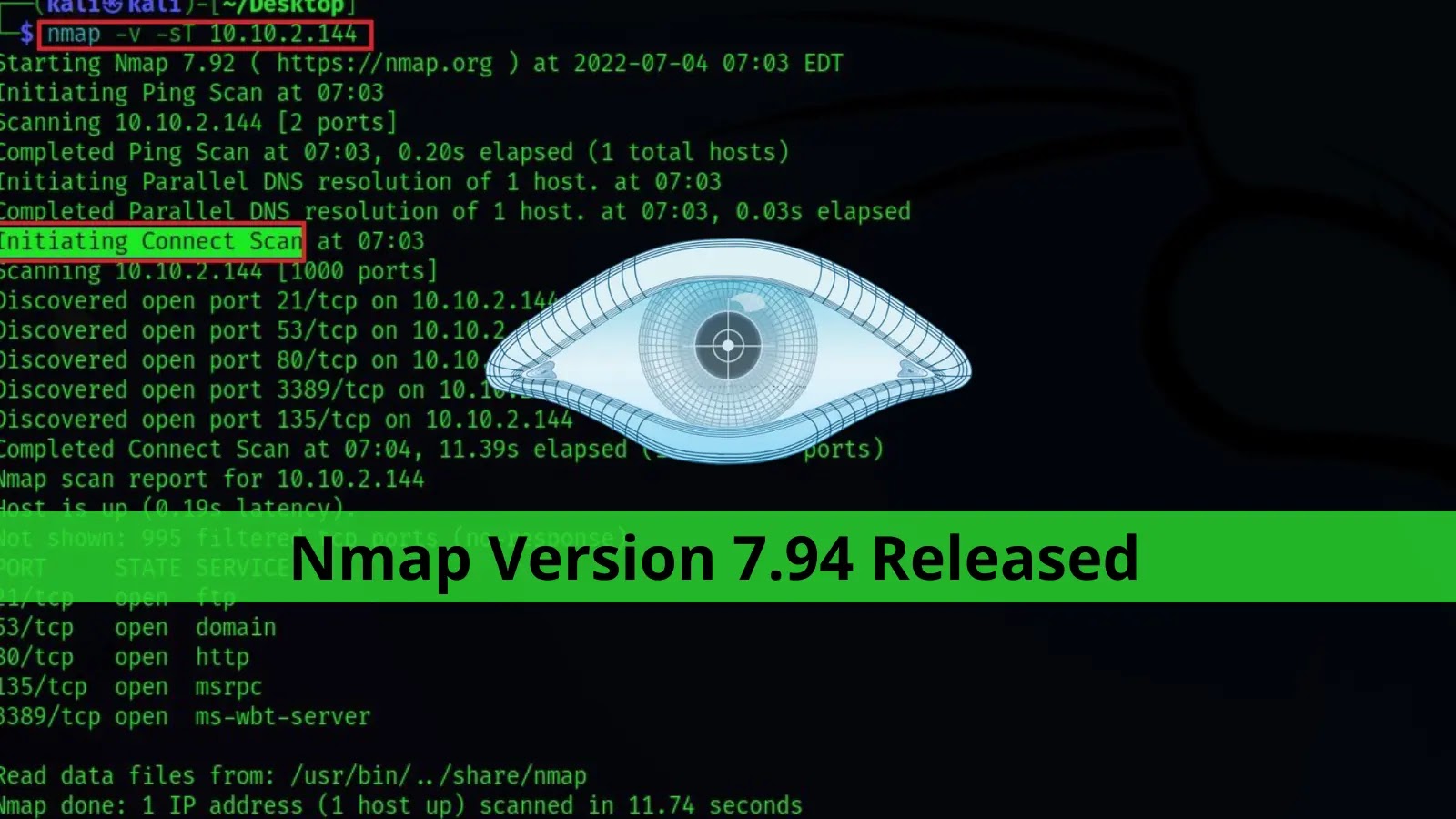
The latest version of Nmap, 7.94, was released on its 26th birthday. The most significant upgrade was the migration of Zenmap and Ndiff from Python 2 to Python 3 across all platforms.
This new version of Nmap 7.94 was upgraded with more than a number of improvements, fixed some of the critical bugs, and added new Npcap, OS fingerprints, NSE scripts/libs, and other enhancements.
What is Nmap?
Nmap is a free and open-source network scanner, Port Scanner, and network Exploration Tool that supports all cross platforms, including Linux, Windows, UNIX, FreeBSD, OpenBSD, Solaris, IRIX, Mac OS X, HP-UX, NetBSD, Sun OS, Amiga, and more.
“Nmap supports Vanilla TCP connect() scanning, TCP SYN (half open) scanning, TCP FIN, Xmas, or NULL (stealth) scanning, TCP ftp proxy (bounce attack) scanning, SYN/FIN scanning using IP fragments (bypasses some packet filters), TCP ACK and Window scanning, UDP raw ICMP port unreachable scanning, ICMP scanning (ping-sweep), TCP Ping scanning, Direct (non portmapper) RPC scanning, Remote OS Identification by TCP/IP Fingerprinting, and Reverse-ident scanning.”
Npcap is based on the discontinued WinPcap library, but it has significantly improved speed, portability, security, and efficiency. Npcap works on Windows 7 and later Windows versions.
The new Nmap 7.94 release not only benefits Windows but also supports cross-platform with a bunch of new libraries’ performance improvements.
Improvements With Nmap 7.94
- Upgraded Npcap from version 1.71 to 1.75
- Nmap now prints vendor names based on MAC address
- Integrated most-submitted IPv4 OS fingerprints
- profile-guided performance improvements
- Added tftp-version script
- Ncat Accept “connections” from multiple UDP hosts
- Updated many libraries: OpenSSL, zlib, Lua, libpcap
- UDP port scan (-sU) and version scan (-sV) now both use the same data source
- Nmap’s service scan (-sV) can now probe the UDP service
- Ncat listen mode with –udp –ssl
- Handle Internationalized Domain Names (IDN)
- Dramatically speed up Ncat transfers
You can find here the complete list of significant changes that applied in Nmap 7.80, and you can also read the Full Nmap tutorial.
Keep informed about the latest Cyber Security News by following us on Google News, Linkedin, Twitter, and Facebook.





.webp)

.webp)